Blog
Stay apprised of our industry-leading research and insights.
Why Is Test Data Management So Important?
In today’s fast-paced digital world, software testing is a crucial aspect of ensuring the quality, performance, and security of any software application. However, using real production data for testing purposes can expose the system to significant risks, such as...
Duck Creek Data Masking in Depth: A Guide
Insurance platforms are data-heavy by design. Customer identities, policy records, payment details, underwriting notes, claims histories. In a Duck Creek ecosystem, that data powers critical business processes across policy, billing, and claims. It also creates...
Data Compliance and Salesforce
Introduction Salesforce remains the top choice for customer relationship management (CRM), with a 19.5% market share. The company provides more than 150,000 organizations with powerful analytics, marketing automation, and business development services. Without a...
Top Test Data Challenges
Over the past few years, automation has become increasingly prevalent as people rely less on manual work. This trend towards digitalization can be seen in the rise of internet banking and online shopping portals, where people can complete tasks like deposits and...
Value Stream Mapping the DevOps Void
Ever wonder why your releases take so long? After all, your company just invested a “zillion” dollars in a whole bunch of great ‘agile’ tools and a cloud framework. Tools that allow you to automatically provision your infrastructure, applications, and data, and ensure...
Environments: The ROI of TEM
Let me start with a question: as a leader in tech, are you satisfied with the budget you have? If I had to guess, I’d say the answer is no. Because of that, calculating the return on investment of the many activities in software development is certainly an invaluable...
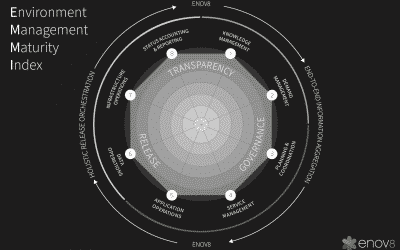
Environment Management Maturity Index Assessment
Ever wondered how mature your IT & Test Environment Management practices are? Well, here at Enov8, over the last few years, we have been building a model called the EMMi (the Environment Management Maturity Index) Originally called the TEMMi, the EMMi is designed...
The Cost of Inefficient Test Environment Management
Do you know how much inefficient Test Environment Management is costing you? One thing that stands out from our discussions with organisations in Asia Pacific, North America and Europe is the distinct lack of awareness when it comes to how much Non Production...
Top 10 Cloud Optimization Tricks
In this digital era, online businesses have become mainstream. Consequently, online commerce has flourished”and led to loads and loads of data! Businesses need to build data centers to store information. Not only that, but if you own a big business, you have to...
Zombie (Ghost) Assets and How to Stop Them
Zombie and ghost assets sound exciting, like a late-night movie you’d watch around Halloween. While in reality they may not be that exciting, they’re scary if you don’t understand and prevent them. The good news is the steps you need to take don’t necessarily...
Test Environments: The Tracks for Agile Release Trains
So, you’ve decided to implement a Scaled Agile Framework (SAFe) and promote a continuous delivery pipeline by implementing “Agile Release Trains” (ART)*. Definition An Agile Release Train is several teams (a portfolio) responsible for the regular release of...
Software Security Anti-Patterns
If you’re like a lot of developers, you might not think much about software security. Sure, you hash your users’ passwords before they’re stored in your database. You don’t return sensitive information in error messages. Each time you log something, you make sure it...
What is a Microservice Catalog? A Detailed Explanation
Microservices have revolutionized the way modern software systems are designed and developed. Breaking down complex applications into smaller, independently deployable services brings numerous benefits in terms of scalability, flexibility, and maintainability....
Marrying SAFe and DevOps
If you work in an organization that uses the scaled agile framework (SAFe), chances are it’s not a small company. It’s enterprise-y. It’s probably gone through some growing pains, which is a good problem to have in the business sense. The good news is that the...
Test Data Management Best Practices (Or TDM Process)
The importance of test data management (TDM) is ever-increasing if you want to avoid data compliance risks and subsequent fines. The combination of enormous fines, such as the one British Airways faced after their data breach, and the overall growing number of...
5 Red Flags Deployment Management Is Failing
It’s a great step when teams deliberately manage their deployments instead of treating them as second-class citizens to writing code. But there are many pitfalls to managing deployments effectively. Many things lurk, waiting to trip us up. We want to start with...
Delphix Alternatives: 7 to Consider in 2026
If you're searching for delphix alternatives, you're likely evaluating your test data management strategy. Delphix is widely recognized for data virtualization and masking, but it is not the only option available. As enterprise environments grow more complex and...
The Pros and Cons of Test Data Synthetics (or Data Fabrication)
Data privacy is one of the most pressing issues in the new digital era. Data holds so much value for normal internet users and for all types of companies that are looking to capitalize on this new resource. To keep data anonymous and private, two types of...
Delivering at Scale: Why SAFe Is Essential for Agile Teams
Your organization is in the midst of an agile transformation. You know that agile is the way to go, and you’re looking forward to, or maybe already reaping, some of the benefits. Who can argue with what agile brings to the table? Here’s a short, and incomplete, list...
Test Data Management Strategy Design: Guide & Best Practices
Before software goes into production, it needs to undergo thorough testing to ensure quality and performance. To accomplish this, DevOps teams typically rely on test data. Read on for an overview of test data, including why test data management is imperative for...
Ready to Accelerate Your Delivery?
Let’s build your roadmap to success. Schedule a personalized consultation with our experts to identify your biggest opportunities for automation and efficiency.