The Crucial Role of Runsheets in Disaster Recovery
March, 2024
by Jane Temov.
Jane Temov is an IT Environments Evangelist at Enov8, specializing in IT and Test Environment Management, Test Data Management, Data Security, Disaster Recovery, Release Management, Service Resilience, Configuration Management, DevOps, and Infrastructure/Cloud Migration. Jane is passionate about helping organizations optimize their IT environments for maximum efficiency.
Disaster recovery plans (DRPs) are pivotal for organizations to counteract the effects of unforeseen incidents and ensure business continuity. Within these plans, runsheets are vital, providing detailed procedures for executing recovery tasks efficiently.
Innovate with Enov8
A Platform of Insight
Managing your IT & Test Environments, Releases & Data.
This post highlights the importance of runsheets in DRPs, explores optimization strategies for DR Managers, and introduces the benefits of implementing Enov8 Runsheets Automation for improved operational efficiency.
Enhancing DR with Enov8 Runsheets Automation
Enov8 Runsheets Automation streamlines IT teams’ operational processes, defining automation steps, integrating with DevOps tools, and offering real-time process visibility. This tool not only saves costs but also allows for continuous process improvement.
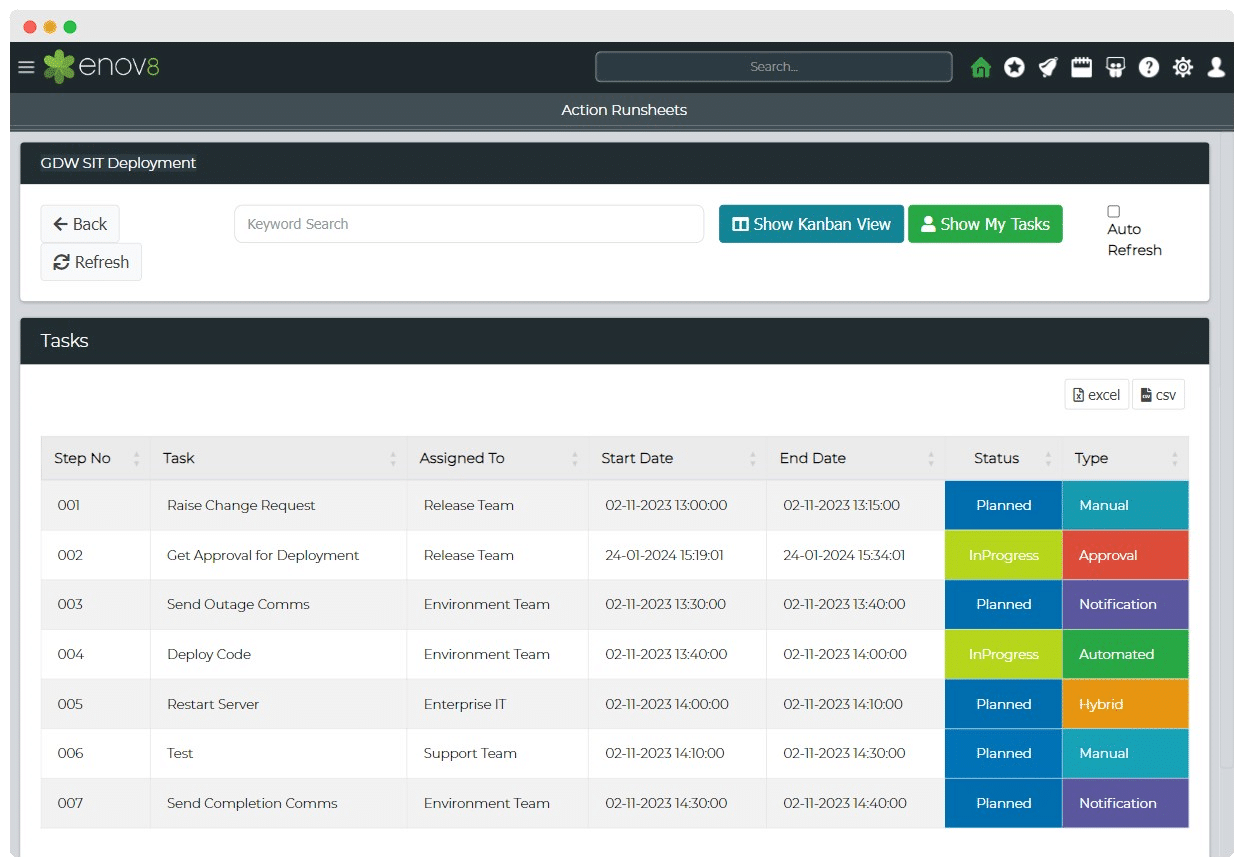
Implementing Enov8 Automation
- Runsheet Creation: Detail the operational steps necessary for recovery.
- Execution: Utilize Enov8’s automation to carry out steps efficiently, with real-time monitoring.
- Continuous Optimization: Regularly review and enhance runsheets for improved performance.
Conclusion
Incorporating runsheets into disaster recovery plans is crucial for a structured, effective approach to managing crises. By adopting best practices and leveraging tools like Enov8 Runsheets Automation, organizations can significantly enhance their preparedness, reduce downtime, and maintain business operations even in the face of disaster. The integration of clear, accessible runsheets and the strategic use of automation will fortify an organization’s disaster recovery efforts, ensuring resilience and continuity.
Relevant Articles
Snowflake Data Masking Explained: A Complete Guide
Most companies don’t realize how many copies of sensitive data they’ve created until it becomes a problem. A single Snowflake environment can contain customer, financial, employee, and analytics data all at once. And once that data gets copied into development or...
What Is an AI Control Tower? A Complete Enterprise Guide
As enterprise AI environments continue to grow, many organizations are looking for better ways to manage visibility, governance, workflows, and operational coordination across increasingly complex systems. That’s where AI control towers come in. In this post, we’ll...
MariaDB Data Masking: Methods, Challenges, and Best Practices
Organizations need realistic data for testing and development, but using raw production data in non-production MariaDB environments can create serious security and compliance risks. MariaDB data masking helps solve this by replacing sensitive information with...
10 Data Masking Solutions to Know About In 2026
A single exposed dataset can create massive compliance, security, and operational headaches for an organization. The problem is that development and QA teams still need realistic data to properly test applications, validate releases, troubleshoot issues, and support...
MySQL Data Masking: Methods, Techniques, and Best Practices
Organizations rely on MySQL databases to run applications, analytics, and core systems. But because these databases often contain sensitive customer and financial data, copying production data into test environments creates risk. That’s where MySQL data masking comes...
What Is AI Data Governance? A Complete Enterprise Guide
AI is rapidly becoming embedded across enterprise systems, from customer service automation to predictive analytics and decision support. But as organizations scale AI, a critical gap is emerging: most do not have clear control over the data that powers their models....