How to Reduce Environment Downtime
by Rohit Gupta
In today’s world, generally IT Operations are outsourced to multiple vendors. On top of the process defined by the organisation, each vendor also brings in their own set of processes and tools for managing their Test Environment. As a test environment manager, you need to review these processes and understand which ones have been successful and which one needs improvement or modification.
Also, you need to check the existing implemented projects to understand if these processes were followed properly. Each process should be documented with all dependencies on systems and audited in time for better control. Doing a health check on the processes help the organisation in improving and bringing new changes, which leads to growth and better test environment management.
Enov8 EcoSystem allows the organisations to view their processes from different perspectives and enables them to understand their dependencies. It also allows environment managers how to conduct impact analysis in case of a failure in processes or systems. Enov8 EcoSystem has in built audit & reporting capabilities which, give alerts if action is required.
User Access Management
Data Integrity is one of the crucial elements in test environment management. Wrong data can lead to application failures, which results in environment downtimes. Additionally, unauthorized access to environments can lead to wrong code or configuration version deployments/changes, which can also result in environment breakage.
To avoid this downtime, proper user access control should be in place throughout test environments. User access also needs to be audited from time to time so that only the right users have access to make changes to environments and data. This will lead to better test environment control and increase in availability.
As part of July 2017 release, enov8 ecosystem has implemented a new User Access Management Module which enables organisations in controlling and auditing their user access across environments. It has in built reports & dashboards which helps in better management of user access.
Contention Management
In today’s faced paced market, each organisation is at its toes to deliver the products in the market. This means lots of projects running in parallel with different requirements. These requirements sometimes lead to contention with other projects for the same systems or environments. Misunderstanding of these contentions can lead to overriding changes in the same environment, which results in downtime for the projects; thus missing crucial timelines. To control these types of downtimes, an environment manager needs to have a complete view of these requirements and contentions.
Enov8 EcoSystem environment and release management module allows the organisations to track contentions not only from environment perspective but also from the requirements perspective with comparison to another project. The advanced level reporting allows the projects to understand if there is any gap in their requirements which they have missed as part of their analysis.
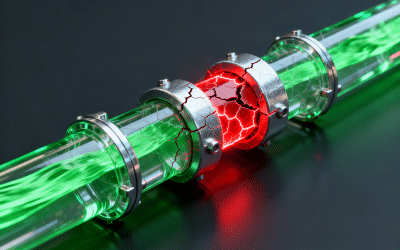
ITSM Processes
In our recent survey, we found that more than 80% of the organisations did not have a proper ITSM solution for test environments, in comparison to production environments. There was no proper change process in place for test environment which lead to chaos, resulting in downtime. Therefore, organisations need a proper CMDB solution along with ITSM for managing their test environments configurations.
Enov8 provides inbuilt ITSM capabilities to organisations. It also allows integration with an organisation’s existing ITSM products to provide more visibility to their environments. Their visual CMDB and Connectivity views provide users with an end to end view of the whole landscape.
Relevant Articles
MongoDB Clone Database Explained
Every engineering team relies on MongoDB cloning, but very few do it safely at scale. What starts as a simple way to copy data often turns into security risks, rising costs, and inconsistent environments. Cloning a MongoDB database is used to create safe,...
Data Anonymization Tools: 9 to Know About in 2026
A common risk in modern software delivery is using copies of production data for development and testing. These environments rely on realistic datasets but often include sensitive customer, financial, or health data that should not leave production systems. Data...
Postgres Data Masking: A Guide to Securing PostgreSQL Test Data
PostgreSQL stores sensitive data such as customer profiles, financial transactions, and authentication records. This data is often copied into lower environments for development, testing, and analytics. The issue is that these environments aren’t designed to safely...
Data Poisoning vs. Poor Data Preparation: The Enterprise AI Risk Comparison
There is a pattern that repeats itself whenever a new technology becomes strategically important to the enterprise. First, adoption outpaces understanding. Then, when something goes wrong — a breach, a failure, a scandal — the industry scrambles to retrofit governance...
PII Risk in AI Is an Architecture Problem
AI is moving rapidly from experimentation into enterprise scale. Use cases are expanding, agents are emerging, and data is being pushed into pipelines at increasing speed. At the same time, organisations are trying to keep up with the associated risk. The response is...
What Is Enterprise Architecture Governance? A Complete Guide
Enterprise architecture rarely fails because of bad technology. It fails because of too many good decisions made in isolation. Modern enterprises operate across cloud platforms, SaaS tools, legacy systems, APIs, and data environments that evolve independently. This...