Ansible : How do I protect sensitive data with encrypted files
MAR, 2023
by Jane Temov.
Jane Temov is an IT Environments Evangelist at Enov8, specializing in IT and Test Environment Management, Test Data Management, Data Security, Disaster Recovery, Release Management, Service Resilience, Configuration Management, DevOps, and Infrastructure/Cloud Migration. Jane is passionate about helping organizations optimize their IT environments for maximum efficiency.
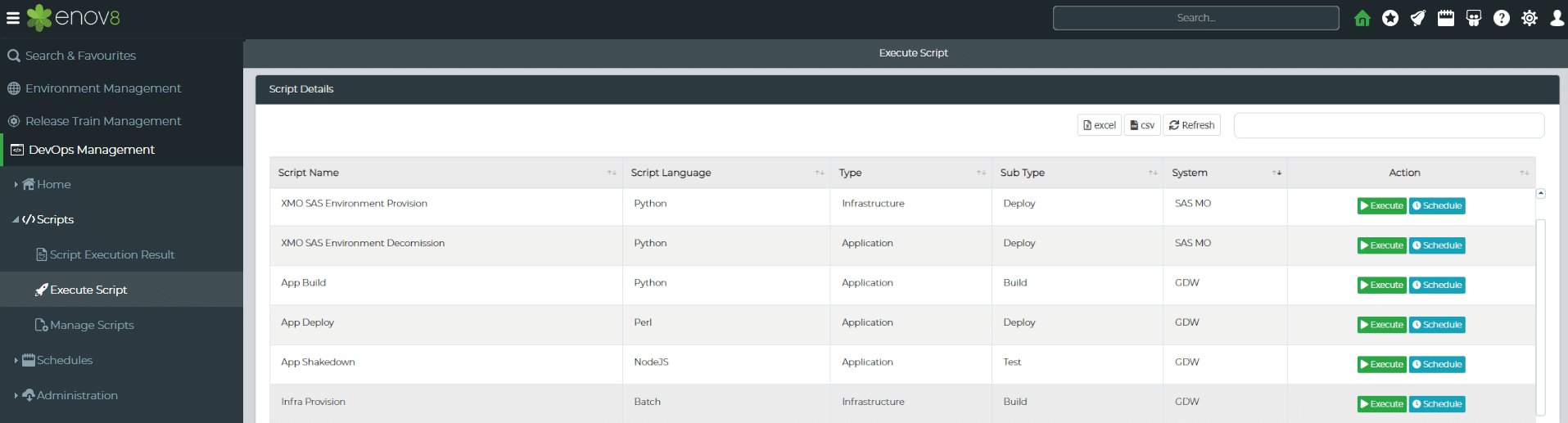
One of the great things about Enov8 Environment Manager is our DevOps Management area. An area that allows you to add your favourite automation independent of language. This includes the ability to “plug in” some very cool IT Automation tools like Ansible.
Enov8 IT & Test Environment Manager
*Innovate with Enov8
Streamlining delivery through effective transparency & control of your IT & Test Environments.
Ansible is an open-source automation tool used to manage and configure systems and applications. It uses a simple and powerful language to describe and automate IT workflows, making it easy to manage complex systems and processes with ease. Ansible is agentless, meaning it does not require any software or daemons to be installed on remote hosts, making it easy to deploy and use. With Ansible, IT teams can automate tasks such as configuration management, application deployment, and orchestration, allowing them to improve efficiency, reduce errors, and improve overall infrastructure reliability.
Protecting Sensitive Data with Encrypted Files
To protect sensitive data with encrypted files or elements in Ansible, you can use Ansible Vault. Ansible Vault is a feature in Ansible that allows you to encrypt sensitive data using a password, and then decrypt it when needed during playbook execution. Here are the steps to use Ansible Vault:
- Create a file that contains sensitive data, such as passwords, API keys, or private keys. For example, let’s say you have a file named
secrets.ymlthat contains the following:
username: myusername
password: mypassword
- Encrypt the file using the
ansible-vaultcommand:
ansible-vault encrypt secrets.yml
This will prompt you to enter a password that will be used to encrypt the file.
- Edit your playbook to include the encrypted file.
For example, let’s say your playbook includes the following task:
# yaml
“ name: Configure the server
become: yesvars:
my_username: “{{ username }}”
my_password: “{{ password }}”template:
src: template.j2
dest: /etc/config.cfg
You can replace the username and password variables with the encrypted values by modifying the task as follows:
# yaml
“ name: Configure the server
become: yes
vars_files:
“ secrets.yml
vars:
my_username: “{{ username }}”
my_password: “{{ password }}”
template:
src: template.j2
dest: /etc/config.cfg
Note that we added the vars_files option to include the encrypted file.
- Run your playbook using the
ansible-playbookcommand and provide the password for the encrypted file:
python ansible-playbook playbook.yml –ask-vault-pass
This will prompt you to enter the password* you used to encrypt the file.
Once you enter the password, Ansible will decrypt the file and use the values in your playbook.
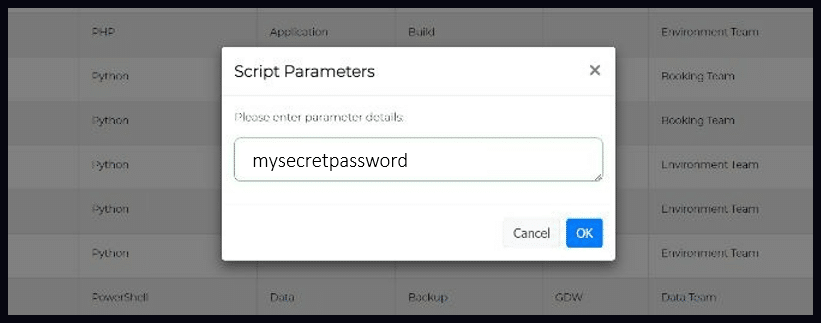
Tip: *Parameterising the Ansible Secret
If you need to parameterise the secret then you can pass the password for the encrypted file as a parameter to the ansible-playbook command using the –vault-password-file option. For example, if your password is mysecretpassword, you can run the following command: ansible-playbook playbook.yml –vault-password-file=/path/to/password_file where /path/to/password_file is a file containing your password, such as: mysecretpassword. This can be particularly useful when you need to run the Enov8 environment automation on a schedule.
With these steps, you can protect sensitive data in your Ansible playbooks using Ansible Vault.
Enov8, DevOps Manager: Screenshot
Conclusion
In conclusion, Ansible Vault provides a powerful and flexible way to protect sensitive data in Ansible playbooks and configuration files. By encrypting sensitive data using strong encryption algorithms and protecting the decryption key with a password or key file, Ansible Vault helps ensure that critical data such as passwords, API keys, and other secrets are kept secure and confidential. Ansible Vault also integrates seamlessly with the rest of the Enov8 & Ansible automation framework, making it easy to incorporate secure credential management into your overall infrastructure management workflow. Overall, Ansible Vault is an essential tool for any organization that wants to ensure the security and integrity of its IT infrastructure and data.
Other TEM Reading
Interested in reading more about Test Environment Management. Why not start here:
Enov8 Blog: Your Essential Test Environment Management Checklist
Enov8 Blog: What makes a good Test Environment Manager
Enov8 Blog: Understanding the Types of Test Environments
Relevant Articles
Snowflake Data Masking Explained: A Complete Guide
Most companies don’t realize how many copies of sensitive data they’ve created until it becomes a problem. A single Snowflake environment can contain customer, financial, employee, and analytics data all at once. And once that data gets copied into development or...
What Is an AI Control Tower? A Complete Enterprise Guide
As enterprise AI environments continue to grow, many organizations are looking for better ways to manage visibility, governance, workflows, and operational coordination across increasingly complex systems. That’s where AI control towers come in. In this post, we’ll...
MariaDB Data Masking: Methods, Challenges, and Best Practices
Organizations need realistic data for testing and development, but using raw production data in non-production MariaDB environments can create serious security and compliance risks. MariaDB data masking helps solve this by replacing sensitive information with...
10 Data Masking Solutions to Know About In 2026
A single exposed dataset can create massive compliance, security, and operational headaches for an organization. The problem is that development and QA teams still need realistic data to properly test applications, validate releases, troubleshoot issues, and support...
MySQL Data Masking: Methods, Techniques, and Best Practices
Organizations rely on MySQL databases to run applications, analytics, and core systems. But because these databases often contain sensitive customer and financial data, copying production data into test environments creates risk. That’s where MySQL data masking comes...
What Is AI Data Governance? A Complete Enterprise Guide
AI is rapidly becoming embedded across enterprise systems, from customer service automation to predictive analytics and decision support. But as organizations scale AI, a critical gap is emerging: most do not have clear control over the data that powers their models....